Today almost all people use Wi-Fi internet while on the go. They check out latest news, check transport schedules, watch videos and even conduct business while moving. In some places the internet coverage can be limited and not all people have mobile data turned on their smartphones to do what […]
Search Results for "password"
How HTTPS Websites Help with Security and Ranking?
We have turned digital. From conducting purchases/selling to availing/delivering services, we make use of the internet every day or almost every other day. With such digitization, the security of each online buyer and seller becomes a major concern, especially when the virtual world is prone to data thefts & breaches. […]
The Best Android 10 Features to Know About
Android 10 was released on 3rd September 2019 as the 10th major release of the popular operating system. Asia, and more specifically India, has been the choice of the Android market. There are plenty of Android app development companies in India, and so are the Android app developers. The latest […]
GetInsta: Get Instagram Followers and Likes – App Review
If you are a user who has a personal or commercial Instagram account, then perhaps the first thing you want to do is to bring real followers to your account and a steady stream of likes and comments to your content in order to increase its popularity and ensure that […]
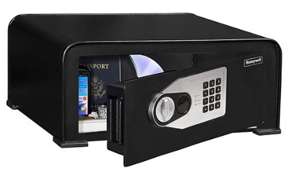
How to Find the Best College Dorm Safe for Your Needs
So, you are getting ready to go off to college. You have set yourself up with a nice dorm room on campus and you’re really looking forward to studying hard towards your goals. However, there is one thing that is bugging you…how do you keep all your belongings secure and […]
The Advantages of a VPS-SSD (Virtual Private Server – Solid State Drive) Hosting
When it comes to web hosting, there are many different options you can think of. Each of them has its own advantages, features, and prices. Today we will take a closer look at what VPS SSD means. A VPS offers the benefits of a dedicated server: root access and the […]
How Blockchain Technology is Disrupting the Mobile App Development Process?
Microsoft which have embedded blockchain in their business model is enjoying its commendations. How Blockchain Impacts Mobile App Development? Today, blockchain is used by many mobile application development companies as it offers better security features to deal with complex transactions. Telecom company collaborates with blockchain mobile app development company that […]
Compress the PDF Files at Ease with PDFelement Pro
Compressing PDF files is most of the time necessary as it involves a reduction in the size of a PDF image so as to make it compatible across a wide range of platforms and operating systems as well as local processes. The different processes are attaching to emails, printing and […]
What is a VPN Tunnel and How It Helps Your Connection
VPN is all about securing your data to let you access the world of the internet with complete freedom. It means that when you use a VPN, there is no fear of being intercepted by the government, ISP or any hacker. A VPN is not something that follows a magic […]
Security Considerations When Using Public Wi-Fi Spots
Today almost all people use Wi-Fi internet while on the go. They check out the latest news, transport schedules, watch videos and even conduct business while moving. In some places, the internet coverage can be limited and not all people have mobile data turned on their smartphones to do what […]
7 Main Steps to Secure your Home Wireless Network
The world is quickly turning into a global village, thanks to technological innovations like digitization and the internet of things (IoT). In the same breath, many households today feature Wireless Home Network (Wifi) connectivity via routers for Internet access. A Home Wireless Network brings unequaled convenience in Internet access and […]
Importance of HIPAA Compliant Healthcare Apps for Your Enterprise
What can be the cost of stolen medical records? Well, it is literally not possible because each medical record means a lot to an individual, a patient. From blackmailing patients to accomplishment of mela fide objectives, any breach of the data can remain harmful to the victim. Here is where […]