Corporate networks are evolving, but security models are not keeping up. Too often, corporate network security architectures are focused on the organization’s dwindling on-site IT infrastructure rather than the network as a whole. Organizations should deploy a modern network security solution, such as Secure Access Service Edge (SASE) to ensure that network security does not compromise network performance and usability.
Traditional Security Is Designed for On-Premises Infrastructure
Historically, most of an organization’s IT infrastructure was located on-premises. Data and applications were housed in on-site datacenters, and employees worked from their offices on computers directly connected to the corporate LAN. This centralization of IT infrastructure resulted in a similarly centralized security model. Most organizations have historically used a perimeter-focused security model.
Under this model, the organization fortifies the network perimeter, deploying firewalls and other security solutions to enforce the boundary and block any malicious content that attempts to cross it. This made it possible to use a simple trust model where everything inside the network is considered “trusted”, and attacks are assumed to have to cross the network perimeter, where they can be detected and blocked before they reach the internal, protected network.
IT Infrastructure Is Increasingly Moving Off-Site
While, historically, the majority of an organization’s IT infrastructure was located on-premises, this is becoming less and less true over time. In recent years, IT infrastructure has moved off-premises for a number of different reasons:
- Cloud Deployments: Organizations are increasingly moving important data and critical applications to cloud-based infrastructure. This infrastructure provides a number of benefits to an organization – including improved scalability, flexibility, and cost – but involves moving key functionality off-premises to cloud provider-controlled infrastructure.
- Remote Workers: COVID-19 accelerated an existing trend of employees working from outside of the office. Many organizations have realized that supporting a telework program is not only possible but also benefits the company in a number of different ways. As a result, employees are increasingly working remotely, rather than from the office on devices connected to the corporate LAN.
- Mobile Devices: Even employees working from the office are becoming less dependent on devices connected to the corporate Ethernet. The rise of mobile devices means that employees may be performing business activities on devices connected to mobile networks or non-corporate Wi-Fi. This means that, even if an employee is on-site, they might be using a very different network infrastructure.
- Internet of Things (IoT) Devices: IoT devices are becoming popular even in business contexts, and the advent of 5G is likely to only accelerate this trend. Like mobile devices, this means that systems collecting and processing sensitive corporate data will be connected directly to the public Internet.
All of these changes boil down to a single major shift for corporate networking. Instead of being the core of an organization’s network traffic, the corporate LAN is only one node among many in the corporate WAN.
Security Should Be Designed for the Majority, Not the Exception
The corporate network is expanding, and users and corporate systems are increasingly outside of the traditional network perimeter. However, many organizations’ approach to cybersecurity has not kept up with this trend.
A desire to stick with the “tried and true” and leverage existing security investments has resulted in organizations adopting inefficient approaches to network security. Instead of moving security to the network edge and securing the enterprise WAN, these organizations divert all traffic through the on-premises network for security inspection before forwarding it on to its destination.
While this ensures network security, it does so at the cost of network performance and scalability. Routing all traffic through the headquarters network has significant impacts on traffic latency due to the inefficient routing and delays caused by overloaded network infrastructure. Additionally, such a network scales poorly as the headquarters network becomes a single point of failure in the corporate WAN. Instead of attempting to make modern networks fit legacy security infrastructures, organizations must evolve to make security serve the organization. Moving security to the network edge and reducing dependence on the headquarter’s network creates a network that is both usable and secure.
SASE Secures the Modern Enterprise Network
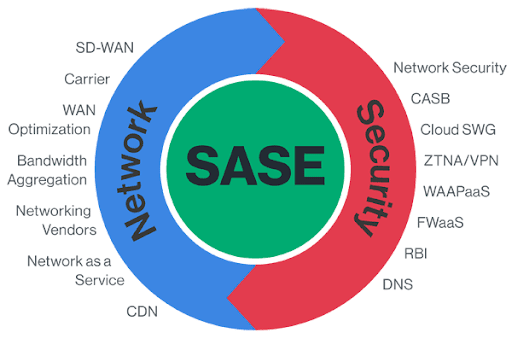
The evolution of the corporate WAN is why SASE is hailed as the future of network security. SASE is designed as an edge-focused security solution that removes an organization’s dependence on on-premises security appliances.
SASE is deployed as a network of SASE Points of Presence (PoPs) deployed in the cloud as a virtual appliance. Each SASE PoP incorporates both SD-WAN functionality and a full security stack. This enables it to optimally route traffic between SASE PoPs and perform full security inspection of all traffic passing through the corporate WAN, regardless of the route that it travels.
Since SASE is implemented as a virtual appliance, SASE PoPs can be deployed geographically near an organization’s network endpoints (cloud infrastructure, remote users, branch locations, etc.). This minimizes the routing inefficiency of entering and leaving the WAN through SASE PoPs, and the use of dedicated network links between PoPs minimizes traffic latency.
Legacy security models worked for legacy networks, but are ineffective for the modern enterprise. SASE enables an organization to deploy security that doesn’t inhibit the performance of the network or the organization that relies upon it.